You're in expert hands. Trusted by top companies around the world.
our Benefits
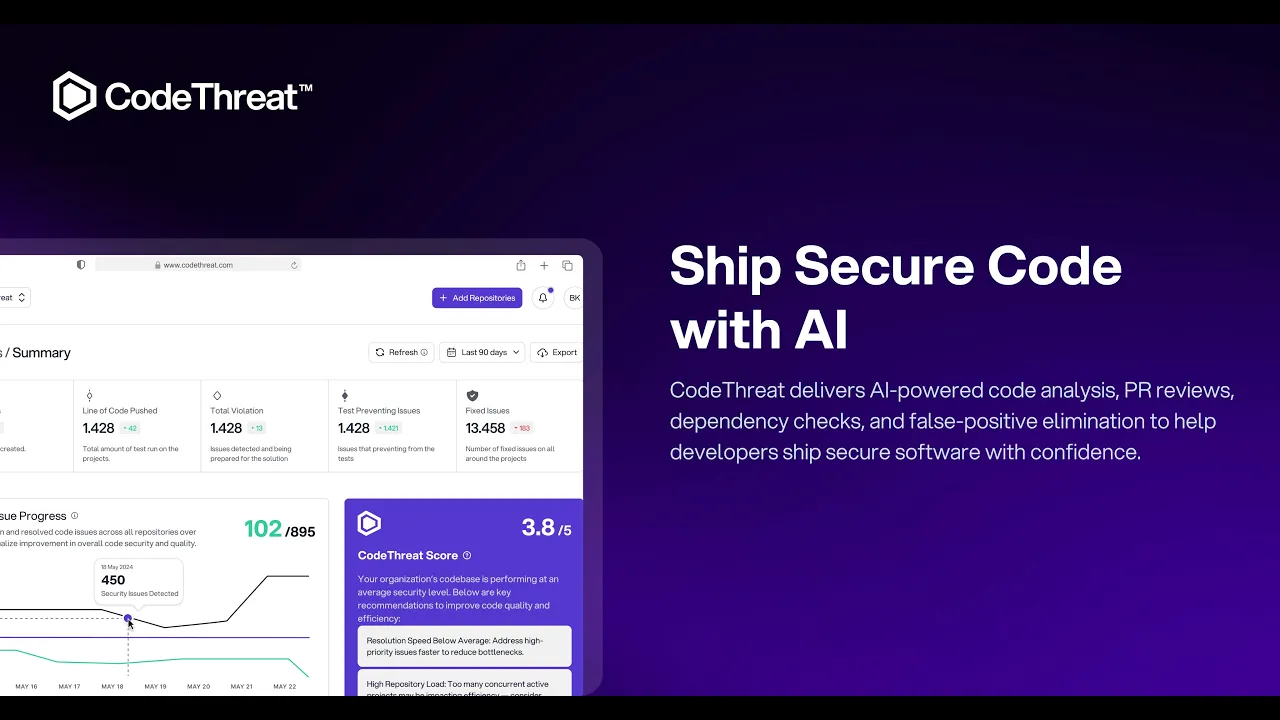
Why Teams Choose CodeThreat
AI agents that understand your code, reduce the noise, and surface only meaningful security findings.
PR Review
Analyzes code changes at pull request level and highlights risks before merge. This makes security a natural step inside code review instead of an after-production step.
False Positive Elimination
Automatically filters out weak and non-relevant findings using continuous learning. You focus only on real security problems instead of wasting time on noise.
AI SAST
Understands your project context to detect complex security issues (logic flaws, data flows, auth paths) that rule-based scanners often miss.
our features
What CodeThreat Offers
Unified security analysis and AI powered code intelligence. All reviews, results and context in one place.


Agentic PR Review
Runs a full project-wide AI review and identifies issues, risks, and improvement points across the entire codebase, similar to how a senior engineer evaluates your project.

False Positive Agent
Re-checks findings, flags non-exploitable ones, and explains why they’re likely false positives, reducing noise before developers lose time.

Agentic Repo Analysis
Maps your entire project and generates AI-powered insights on architecture, documentation, endpoints, dependencies, and data flow for rapid understanding.

AI SAST
Performs an AI-driven review of your entire codebase, identifying issues, risks, and improvement points across the project with clear context.

Repo Mapping
Visualizes your whole repository, linking components, flows, and relationships so teams instantly understand structure without manual effort.
Integration
Broad Language and Integration Coverage
Supports 27+ programming languages and frameworks. Integrates with GitHub, GitLab, Bitbucket, CI/CD pipelines, and cloud providers no workflow change needed.
special features
SAST, SCA, IaC, Container Security and Secret Scanning all in one place, no more tool switching or complex integrations. Everything you need to secure your codebase lives here.
Pricing Plan
Simple pricing plan
No surprise fees, no commitment. Start free — scale only when you need more AI power.

Pro Plan
For teams shipping secure code at scale.
$39
/Per Contributor/Month
Role Based Access Control
Secret Scanning
Infastructure Security
Jira Integration
Vulnerability Report & Exports





























